In v2026.1 we introduced support for a more robust and real-life secure authorization for your FHIR endpoints.
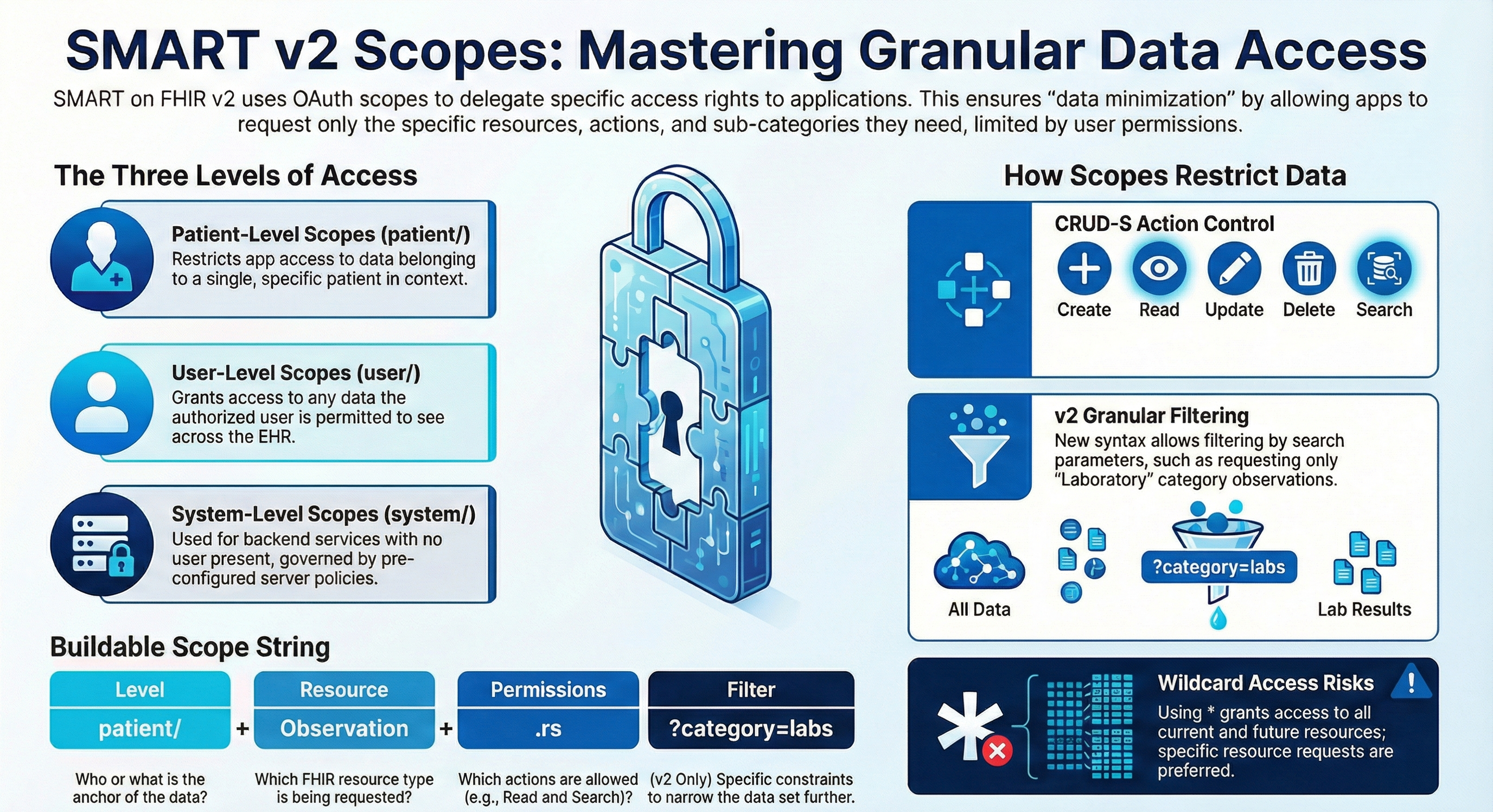
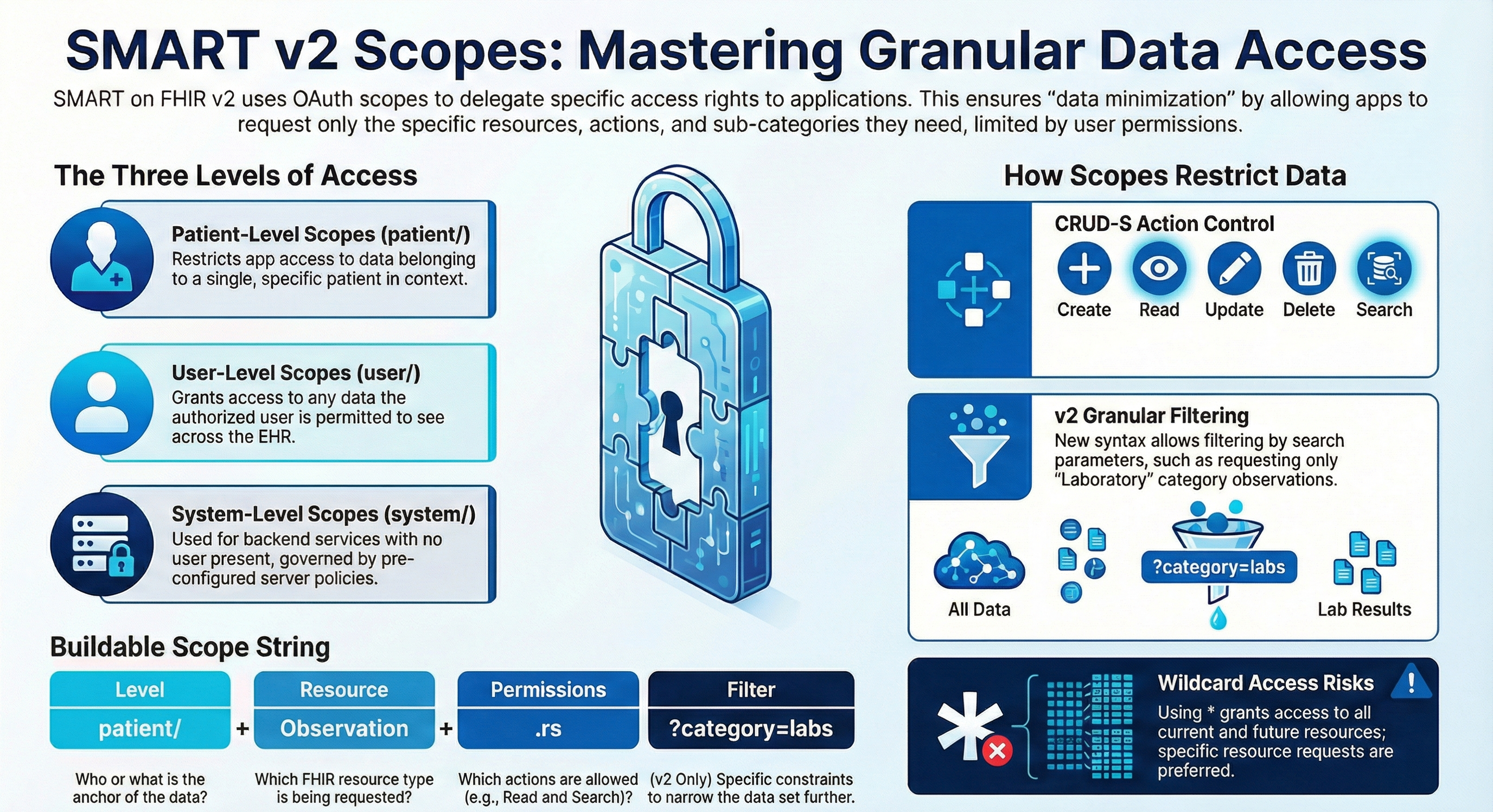
This is achieved by using SMART on FHIR v2 fine-grained scopes.
Security in IT is the protection of computer systems from the theft and damage to their hardware, software or information, as well as from disruption or misdirection of the services they provide.
In v2026.1 we introduced support for a more robust and real-life secure authorization for your FHIR endpoints.
This is achieved by using SMART on FHIR v2 fine-grained scopes.
. . . you are not alone.
Help is available.
This took me a while to figure out, and I assume there may be others struggling too. I made my way through all the Entra stuff to set up a client credentials workflow to send email through a Microsoft 365 account. I was able to successfully retrieve my token, but I couldn't ever get it to authenticate with the SMTP server using the %Net.SMTP class. There were two parts to fixing this.
First, the authenticator's access token needs to be more than JUST the access token. It has to be formatted as:
set smtp.A very important feature for HL7 FHIR has been introduced with the release of v2026.1 - the support for SMART on FHIR v2 fine-grained granular Scopes.
This enables you to be much stricter and more accurate in the access you provide to the data in your FHIR repository.
Part of this new support is to refuse requests that don't match the scopes, but an even more interesting ability is to filter the results according to the provided scopes.
This article reflects my recent experiences at trying to connect an IRIS Business Operation to a secure Kafka Server, using SSL tunnels to encrypt the communications and using SASL (Simple Authentication and Security Layer) password hashing with SCRAM-SHA-512.
Hi Community,
Enjoy the new video on InterSystems Developers YouTube:
⏯ Resilience by Design - Business Continuity Through Secure Backup @ Ready 2025
Hi folks!
Is there an easy setting, e.g., to merge.cpf so that it will disable the management portal on a deployed IRIS container?
The idea is to let only one of my particular web apps be available and everything else not even accessible on IRIS.
Hi Community,
Enjoy the new video on InterSystems Developers YouTube:
⏯ Operationalizing Cybersecurity - Making it Real and Relevant @ Ready 2025
Hi Community,
Enjoy the new video on InterSystems Developers YouTube:
⏯ Data on the Move - Securing InterSystems IRIS Connections with TLS @ Ready 2025
Hi Community,
Enjoy the new video on InterSystems Developers YouTube:
⏯ Ahead of the Threats - The Future of Secure Systems @ Ready 2025
Hello Community!
We're pleased to invite you to the upcoming webinar in Hebrew:
👉Getting Started with OAuth 2.0 on InterSystems👈
📅 Date & time: March 25th, 3:00 PM IDT
SQL injection remains one of the most critical vulnerabilities in database-driven applications, allowing attackers to manipulate queries and potentially access or compromise sensitive data. In InterSystems IRIS, developers have access to both Dynamic SQL and Embedded SQL, each with distinct characteristics. Understanding how to use them securely is essential for preventing SQL injection.
Dynamic SQL constructs queries as strings at runtime. While this offers flexibility, it also creates a vulnerability if user input is not handled correctly.
With the release of InterSystems IRIS Cloud SQL, we're getting more frequent questions about how to establish secure connections over JDBC and other driver technologies. While we have nice summary and detailed documentation on the driver technologies themselves, our documentation does not go as far to describe individual client tools, such as our personal favourite DBeaver. In this article, we'll describe the steps to create a secure connection from DBeaver to your Cloud SQL deployment.
.png)
IRIS makes SIEM systems integration simple with Structured Logging and Pipes!
IRIS can use a KMS (Key Managment Service) as of release 2023.3. Intersystems documentation is a good resource on KMS implementation but does not go into details of the KMS set up on the system, nor provide an easily followable example of how one might set this up for basic testing.
The purpose of this article is to supplement the docs with a brief explanation of KMS, an example of its use in IRIS, and notes for setup of a testing system on AWS EC2 RedHat Linux system using the AWS KMS. It is assumed in this document that the reader/implementor already has access/knowledge to set up an AWS EC2 Linux system running IRIS (2023.3 or later), and that they have proper authority to access the AWS KMS and AWS IAM (for creating roles and polices), or that they will be able to get this access either on their own or via their organizations Security contact in charge of their AWS access.
What is JWT?
JWT (JSON Web Token) is an open standard (RFC 7519) that offers a lightweight, compact, and self-contained method for securely transmitting information between two parties. It is commonly used in web applications for authentication, authorization, and information exchange.
A JWT is typically composed of three parts:
1. JOSE (JSON Object Signing and Encryption) Header
2. Payload
3. Signature
These parts are encoded in Base64Url format and concatenated with dots (.) separating them.
Hi, Community!
Do you need a way to securely manage your passwords, API keys, and other credentials? See how the Secure Wallet in InterSystems IRIS® data platform can help:
There is a Master Table within IRIS that I am populating from Epic but want to share it with our Enterprise Application Development Team (Web). As a test I was able to use _SYSTEM from postman to execute the following.
POST /api/atelier/v1/xxxx/action/query HTTP/1.1
Host: xxxxxxxx
Content-Type: application/json
Authorization: ••••••
Cookie: CSPSESSIONID-SP-443-UP-api-atelier-=00f0000000000AKyLjBfUvU$MpFD8UT8y$EoNKNw1ixZeXN4_Q; CSPWSERVERID=hzZAT5rb
Content-Length: 86
{"query": "SELECT * FROM osuwmc_Epic_Clarity.Also in previous versions you could define your FHIR Server to accept requests via OAuth 2.0 (e.g. for a SMART on FHIR client) but nowadays with v2024.3, which was released a while ago, there is a new feature, that enables doing this more easily - the OAuth FHIR Client QuickStart.
.png)
.png)
It was encouraging to see more people building VS Code extensions for the recent contest. However I noticed that of of the three extensions requiring credentials with which to make their connections only mine, gj :: dataLoader, leverages the long-established and officially-supported InterSystems Server Manager extension to obtain the connection definitions and to handle credentials securely.
Introduction
In today's rapidly evolving threat landscape, organizations deploying mission-critical applications must implement robust security architectures that protect sensitive data while maintaining high availability and performance. This is especially crucial for enterprises utilizing advanced database management systems like InterSystems IRIS, which often powers applications handling highly sensitive healthcare, financial, or personal data.
Auditing is a critical capability ensuring the security of your server, and for quite a while ago we have included the ability to audit SQL statements run on the server.
With v2024.3 out already we're providing finer-grained options for defining these events to audit.
InterSystems IRIS provides extensive configurable security options, yet many developers primarily use roles and resources to secure entire tables or routines. Today, we will delve deeper. We can also secure individual columns and rows separately, but these two mechanisms operate very differently. Let's begin with the columns.
Column Security
For testing and demonstration, we will keep our table structure concise and straightforward. We have a table called "Person" in the USER namespace that contains an ID column, a date of birth column (DOB), first name, and last name.
Security is fundamental to enterprise application development. InterSystems IRIS provides a comprehensive security framework that protects data, controls access, and ensures compliance. This guide introduces essential security features for developers new to IRIS, covering authentication, authorization, encryption, and practical implementation strategies.
Throughout this guide, we'll use Docker containers to demonstrate security configurations in a practical, reproducible environment.
Parallel query hinting boosts certain query performances on multi-processor systems via parallel processing. The SQL optimizer determines when this is beneficial. On single-processor systems, this hint has no effect.
Parallel processing can be managed by:
Setting the auto parallel option system-wide.
Using the %PARALLEL keyword in the FROM clause of specific queries.The 2025.3 release of InterSystems IRIS® data platform, InterSystems IRIS® for Health, and HealthShare® Health Connect is now Generally Available (GA). This is a Continuous Delivery (CD) release.
Release Highlights:
.png)
A few days before Kubecon, the external-secrets-operator went GA with 1.0.0 and is set to ride shotgun for Kubernetes Secrets Management and put Vault in the backseat. You can glance at the "Providers" list for the solution and immediatley understand that you can leave the "which Secrets Manager" conversation to others while you do your job utilizing external secrets on your IrisCluster workloads, which by my count with the operator and a single IrisCluster is more than a fistful of secrets of different types, even under a single tenant. So let them sprawl, the secrets managers that is, not the secrets.
.png)
Hey Intersystems Community!
I'm trying to get IRIS to serve static files, including security and redirect to login if no session is present.
This is the flow I am trying to accomplish:
For CSP applications this seems to work. I can open "http://localhost:52773/csp/sys/sec/%25CSP.UI.Portal.Applications.Web.zen?
Hello everyone! 👋
I have a question regarding roles and resources.
To give you some context: I have a user who has been assigned only the role %HS_UsageDashboard_Access.This allows them to access the dashboards correctly (by giving the direct URL). Then, if I try to access the Management Portal with this same user, I can log in with no access to any resources within it (as expected).
The point is that I would like to completely deny him access to the Management Portal, while allowing him to view only the dashboards, as expected from the %HS_UsageDashboard_Access role.
HTTP and HTTPS with REST API
Hello
The HTTP protocol allows you to obtain resources, such as HTML documents. It is the basis of any data exchange on the Web and a client-server protocol, meaning that requests are initiated by the recipient, usually a Web browser.
REST APIs take advantage of this protocol to exchange messages between client and server. This makes REST APIs fast, lightweight, and flexible. REST APIs use the HTTP verbs GET, POST, PUT, DELETE, and others to indicate the actions they want to perform.
When we make a call to a RESt API, what actually happens is an HTTP call. The API receives this call and according to the requested verb and path, the API performs the desired action. In the case of the Iris implementation we can see this clearly in the URLMap definition area:
I have an API set up in IRIS which is secured using an IRIS authentication service, so there is a bearer token being passed down in the request header.
I've already set