Hello Community!
We're pleased to invite you to the upcoming webinar in Hebrew:
👉Getting Started with OAuth 2.0 on InterSystems👈
📅 Date & time: March 25th, 3:00 PM IDT
This tag unites all posts related to roles (container that holds one or more privileges for access to SQL Tables), users (identity of the login when it is connected to a database) and authorization (function of specifying access rights/privileges to resources).
Hello Community!
We're pleased to invite you to the upcoming webinar in Hebrew:
👉Getting Started with OAuth 2.0 on InterSystems👈
📅 Date & time: March 25th, 3:00 PM IDT
How to obtain an evaluation license for testing ECP and FHIR in Community Edition 2025.3?
When I was younger (a question about exactly how much younger is outside the scope of this article), the word “token” meant fun. You see, just a couple of times a year, I would get to go to an arcade and play some amusing video games with my friends.
These days, tokens signify security. JSON Web Token (JWT) Authentication has become one of the most popular standards for securing REST APIs. Fortunately for IRIS users, we have a straightforward way to set up applications to be protected this way. Yet, the idea is still similar to my old arcade days.
Validating JSON data against JSON Schema is a common requirement for modern applications. FastJsonSchema brings this capability natively to InterSystems IRIS, combining speed, simplicity, and full schema compliance.
Unlike traditional validation approaches, FastJsonSchema generates native ObjectScript code from your JSON Schemas and compiles it directly to iris object code, enabling idiomatic performance without relying on external libraries or runtimes.
InterSystems IRIS provides extensive configurable security options, yet many developers primarily use roles and resources to secure entire tables or routines. Today, we will delve deeper. We can also secure individual columns and rows separately, but these two mechanisms operate very differently. Let's begin with the columns.
Column Security
For testing and demonstration, we will keep our table structure concise and straightforward. We have a table called "Person" in the USER namespace that contains an ID column, a date of birth column (DOB), first name, and last name.
Security is fundamental to enterprise application development. InterSystems IRIS provides a comprehensive security framework that protects data, controls access, and ensures compliance. This guide introduces essential security features for developers new to IRIS, covering authentication, authorization, encryption, and practical implementation strategies.
Throughout this guide, we'll use Docker containers to demonstrate security configurations in a practical, reproducible environment.
Hello everyone! 👋
I have a question regarding roles and resources.
To give you some context: I have a user who has been assigned only the role %HS_UsageDashboard_Access.This allows them to access the dashboards correctly (by giving the direct URL). Then, if I try to access the Management Portal with this same user, I can log in with no access to any resources within it (as expected).
The point is that I would like to completely deny him access to the Management Portal, while allowing him to view only the dashboards, as expected from the %HS_UsageDashboard_Access role.
I have an API set up in IRIS which is secured using an IRIS authentication service, so there is a bearer token being passed down in the request header.
I've already set
We’re building out a data lake in IRIS 2025.1 that aggregates data across multiple business systems and departments. I’m trying to establish best practices for schema design and separation.
Right now, I’m thinking of using a separate schema for each distinct system of record feeding into the data lake - for example, one schema per upstream source system, rather than splitting based on function (e.g. staging, raw, curated). The idea is that this would make it easier to manage source ownership, auditing, and pipeline logic, especially when multiple domains are contributing data.
Hi all,
I’m working on a data transformation in IRIS where I need to calculate the difference in hours between two timestamps stored as %TimeStamp.
Example:
Set startTime = "2024-07-12 08:30:00"
Set endTime = "2024-07-12 15:15:00"
I’d like to calculate the number of hours (with decimals, like 6.75) between them. What's the recommended way to do this in ObjectScript? I’ve seen examples using $ZDATETIME, but I’m not sure if that’s the cleanest approach.
Any suggestions or best practices would be appreciated!
Thanks,
Jhonn Marie
Is it possible to audit code changes in a namespace?
Ideally what we'd like to be able to do is check which classes were compiled (or deleted) in a time period, eg in last 3 months, and which user made those changes. Even better would be an audit of what those changes were, but that's less important (for us, as we can probably find that information in other ways).
We have a service where 3 groups, each with multiple users, potentially have access to make changes to the live service. With the best will in the world, each group doesn't always tell every other group about changes made.
I am trying to log in to the Web Gateway Management and I have missed placed the password to access the system I have tried
changing the password under local settings in the CSP.ini and that has managed to change the password to access the gateway but cannot log me into the management area I have followed a post here and read here and I seem not to get the answers that actual explain how I can get to the web gateway management.
I'm trying to authorise my app using OAuth 2.0 i Cache. Sadly I'm unable to exchange the authorization code for an access token.
I am able to redirect user to the /authorize page, where the user can login and approve my app. The user is then correctly redirected back to my app and a ?code parameter is sent back.
Hi,
I will try to explain my problem. I have a Main ZenPage on one server that has 2 buttons: each button will launch a different ZenPage on a separate server in an iFrame. All 3 servers have the same user.
Currently, the user logs in to the Main ZenPage, but when they click either button to launch the other ZenPage on the separate server they get the login screen again to login to that server.
Is there anyway I can pass the credentials from the Main ZenPage to the child ZenPages, so that the user doesn't have to login again? Thanks.
“I have been waiting for thirty seconds for service. This is outrageous! I am leaving!”
“I am very sorry to hear that, sir. Perhaps, next time, you should make a reservation.”
If you heard that comment at your favorite restaurant, you would think the person saying it was being ridiculous. However, in the context of your API, it makes perfect sense. Just like your favorite eatery, your API has some regular patrons who, as you know, will be visiting one day or another. It would be great to be able to make a standing reservation for them as well.
It will involve a couple of IRIS fundamentals.
The ideal number of table permissions to assign for your users is zero. Permissions should be granted upon sign-in based on the application used for access. For web applications, we have a simple way of doing this by appointing application roles, matching roles, and required resources in the System Management Portal.
ODBC and JDBC connections present a different problem, however, especially when third-party applications are involved. As providers of an ERP system, our customers often wish to be able to employ various software packages to integrate with or report on their data. Many of these programs are capable of running any kind of query. Yet, letting them do that can be devastating to a customer’s data.
So far, we have covered how to use ObjectScript to manage users, roles, resources, and applications. There are a few other classes in this package that work similarly to the ones mentioned above. However, these four classes are the ones everyone will have to use to manage their application security. Suppose you wanted to create your own Security management portal for this package. There would be some specific issues to think about for an API. Since the classes use similar methods, we can create fewer API endpoints using indirection.
Here in %SYS, we have already examined users, resources, and roles. Now that we know how to set all of that up, we should give it a purpose. Next we will talk about applications! As you may expect, we will see various identical class methods defined here that we have seen in the previous classes. However, some of them will have some tiny yet significant differences.
I was attempting to find a solution to grant clients anonymous access to certain API endpoints while securing others within my REST API. However, when defining a Web Application, you can only secure the entire application and not specific parts of it.
I scoured the community for answers but didn't find any exact solutions, except one recommendation to create two separate web applications, one secured and the other unsecured. However, in my opinion, this approach involves too much work and creates unnecessary maintenance overhead.
I am trying to lock down security within our Development environment per requirements from a Security Audit that was done earlier this year. I need to try to limit access at a public level, access to cache users, and exposure.
I installed IRIS with the Lockdown method, and have configured my web applications, services, resources, etc.
When I go into my namespace, I am constantly presented with the following error when I try to start or stop an Object...
Cannot login as IRIS manager.
My original ZAUTHENTICATE.mac to use Delegated sign on did not include GetCredentials(), however I am being told it probably should have it so I am eliminate an error I am seeing when trying to troubleshoot the ZAUTHENTICATION. I am trying to add the GetCredentials() from the documentation to the existing ZAUTHENTICATE.mac but I am getting an error
GetCredentials(ServiceName,Namespace,Username,Password,Credentials) Public {
// For console sessions, authenticate as _SYSTEM.
If ServiceName="%Service_Console" {
Set Username="_SYSTEM"
Set Password="SYS"
Quit $SYSTEMStatus.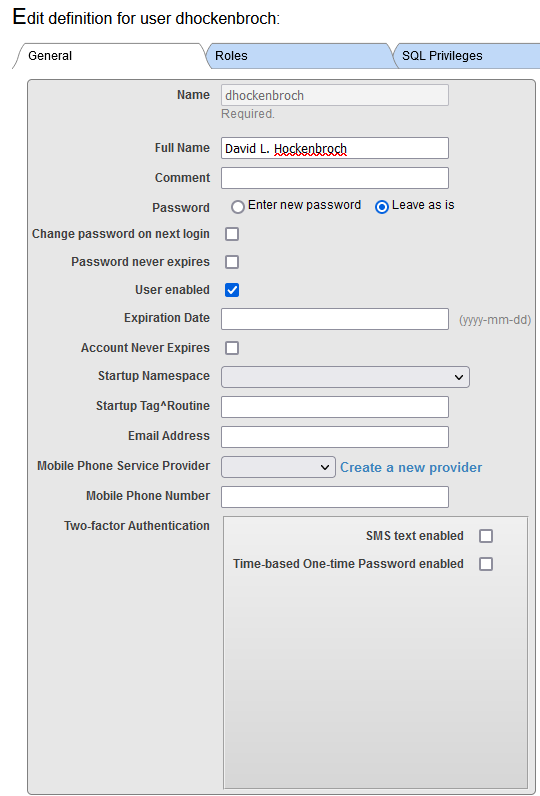 Have you ever thought of creating your own systems for editing users or, perhaps, even an API that you can call? Today, you’re going to join me in the %SYS namespace and get to know Security.Users!
Have you ever thought of creating your own systems for editing users or, perhaps, even an API that you can call? Today, you’re going to join me in the %SYS namespace and get to know Security.Users!
This class has forty properties, many of which you’ve seen before in the System Management Portal. There are class methods for manipulating most of those properties. Every method in this class is a class method, and in most of them, the username is passed as an argument. These methods can be used when you do not want to open and directly manipulate the user’s objects, which is a bad idea anyway!
This question originally appeared in the comments of the article: Git for Shared Development Environments
Hi, @Timothy Leavitt
You wrote:
- Concurrency control for multiple users working in the same environment at the same time. Once you make changes to a class/routine/etc., it's yours until you discard or commit your changes. (We do have ways around this when needed, though!)
I'm trying to find any documentation about "(We do have ways around this when needed, though!)" part, and it looks like it's never mentioned anywhere else apart from the quoted paragraph.
Hey Community,
Tired of entering login-password during the docker build with your InterSystems IRIS every time?
There is a handy way to turn it on and off – use the passwordless zpm module.
Watch this video to explore how to use the passwordless ipm module to turn on and off entering login-password during docker build with your InterSystems IRIS:
Has anyone successfully implemented Multi-factor Authentication for TrakCare?
Recently I had the challenge to create a secure authentication method to authorize access to some data, but unfortunately I had zero experience with those security configurations and I felt that I was missing some basic concepts to have a better understanding of the official documentation.
After studying and managing to deliver the classes that I was asked to develop, I'd like to share a little bit of my new knowledge, which helped me follow the topics in the documentation.
I want to grant access to view the Error Trap in System Management Portal to certain admins, without giving them access to anything that would alter Caché behavior, such as users or database sizes. I was looking for a granular Resource that would do this, but haven't been able to find what I'm looking for.
Secondly, I granted %Developer role to my developers, but they don't appear to be able to use custom menus in Cache Studio until I grant them %All. Is there a granular Resource that I could use to add to a custom Role and grant to them that would allow custom menus in Cache Studio?
When creating a PRA (Privileged Routine Application; which by the way is not relevant just for Routines but also for Classes/Methods), it is important to make sure you include a new $ROLES, before calling AddRoles(). For example:
new $ROLES
set status=$System.Security.AddRoles("MyPrivilegedRoutineApplication")This way you ensure that indeed the added (elevated) roles "evaporate" for the User running this code, once the User is out of the scope of that routine/method.
[Thank you @Andreas Dieckow for validating this]
In our current UCR arhcitecture, we use two installations. We have one machine with Access, Registry and Edges and one machine with the ODS. On the machine with the Registry, I can create a user/clinician. When I log into the management portal with this user, a so-called delegated user is created in the cached users table. So far everything is going well.
When I try the same on the machine with the ODS I get the message : 'ERROR #822: Access Denied' . so no delegated user is created.... Does anyone have any idea where I can find the solution?
In this article, I’d like to present details of which technologies we had been using to develop our application for the IRIS for Health Contest:
ToC:
First let me quickly introduce the application supported by those technologies.