Cache for Windows (x86-64) 2015.1 (Build 429U) Fri Feb 13 2015 14:37:23 EST [HealthShare Modules:Core:12.07.3703 + Linkage Engine:13.04.3703]
Use case: Search an LDAP database from Caché over TLS using Mutual Authentication.
Extract from the %SYS.LDAP documentation:
For a Windows client, make sure you have the CA certificates already loaded in the Certificates(local computer)\Trusted Root Certification Authorities certificate store.




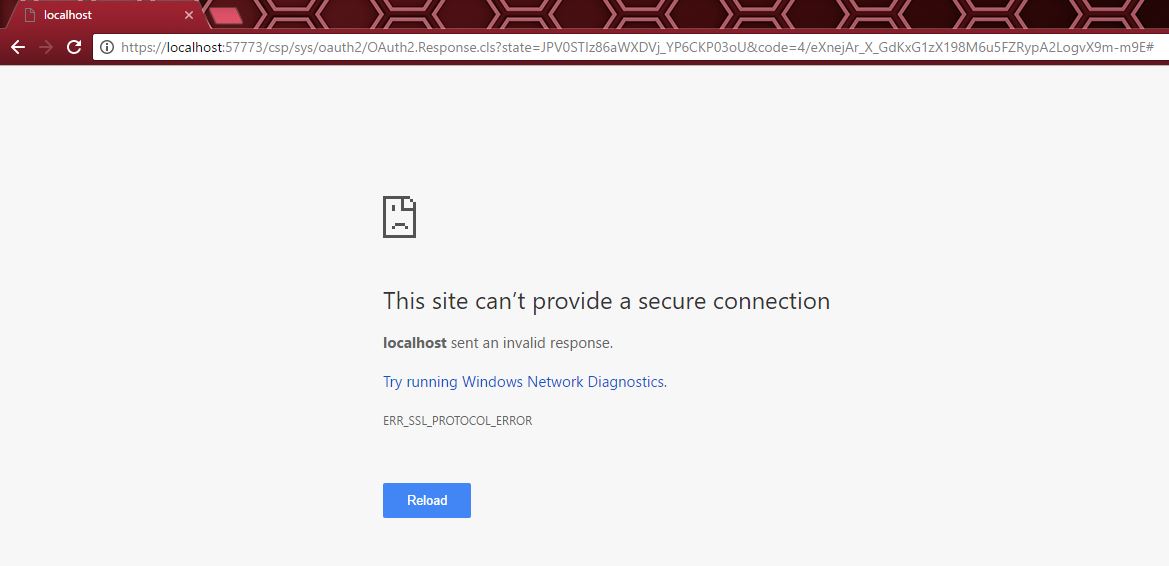 I unable to change response Class.
I unable to change response Class.