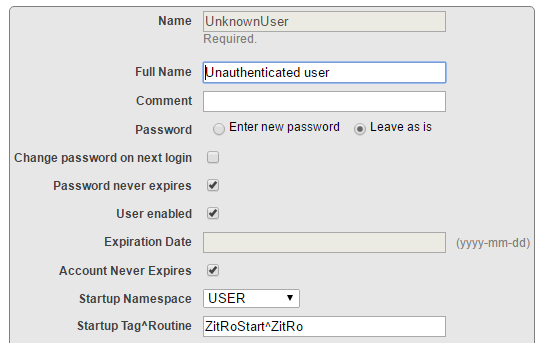
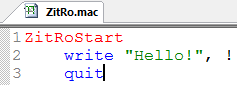
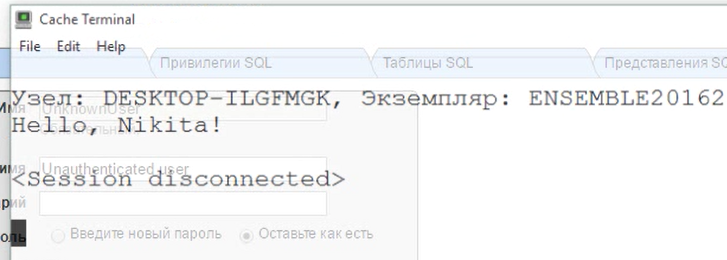
I am working on an ZAUTHENTICATE.mac to move us from local cache users to Delegated Authentication against LDAP.
I have created a user role within my instance of Ensemble that matches the AD Group that I will be assigning everyone in my group to. Is there a way to query the list of available Roles within Ensemble, and if one of my AD groups matches that role, set the role for that user?
How would I compare the AD Group against the Role listing?
Thanks
Scott




 In the
In the