Looking for examples of Cache Password Pattern specifications
Hi -
I know that when specifying Caché password rules (i.e. what constitutes a valid password definition) that the "Pattern Matching" logic is what is getting leveraged under the covers to enforce the "A Password Must conform to X" rule. I was hoping that people could share some more sophisticated pattern matching rules. (in particular, I was wondering what a rule that would require non-repeating mixture of letter, numbers, & punctuation of an overall minimal size)
Comments
Note that NIST has come up with new recommendations about password security, here is a good overview:
https://nakedsecurity.sophos.com/2016/08/18/nists-new-password-rules-wh…
Specifically see this section:
No composition rules. What this means is, no more rules that force you to use particular characters or combinations, like those daunting conditions on some password reset pages that say, “Your password must contain one lowercase letter, one uppercase letter, one number, four symbols but not &%#@_, and the surname of at least one astronaut.”
So it recommends against complex patterns such as the one you are asking about. Also of interest is this one:
No more expiration without reason. This is my favourite piece of advice: If we want users to comply and choose long, hard-to-guess passwords, we shouldn’t make them change those passwords unnecessarily.
The only time passwords should be reset is when they are forgotten, if they have been phished, or if you think (or know) that your password database has been stolen and could therefore be subjected to an offline brute-force attack.
This of course run smack up against "what is being required" of system admins by security departments compared to ACTUAL security. Never confuse useful with required.
Knowing how to force the "less secure, but mandated" patterns is really what my question was about.
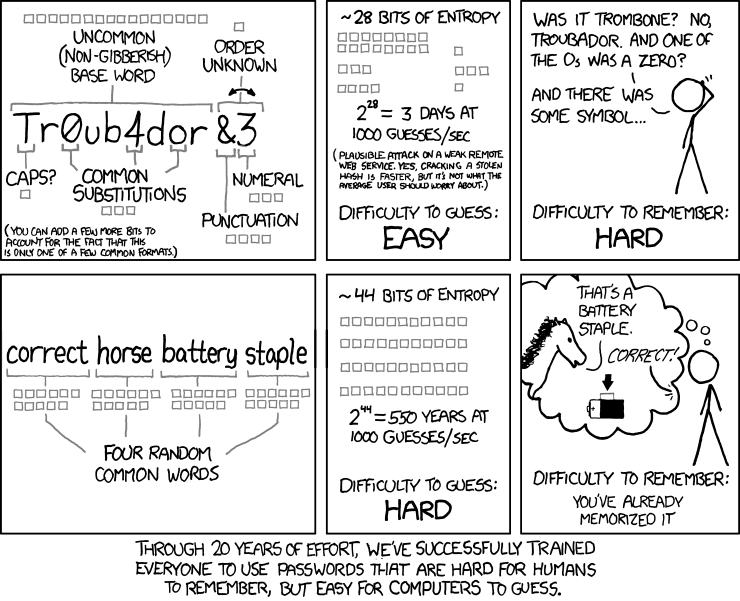
In password security most valuable is entropy.
And a bit of humor about it.
It means, that even if you have a quite hard pattern for the password, but some password will not be strong enough.
On the internet, you can find some online calculators, for the password, when you can check how different symbols change difficulty. For example http://www.passwordmeter.com/