Security wanted!
Welcome to the next InterSystems online programming competition:
🏆 InterSystems Security Contest 🏆
Duration: November 15 - December 05, 2021
Prizes: $9,450 in prizes!
.png)

Security in IT is the protection of computer systems from the theft and damage to their hardware, software or information, as well as from disruption or misdirection of the services they provide.
Security wanted!
Welcome to the next InterSystems online programming competition:
🏆 InterSystems Security Contest 🏆
Duration: November 15 - December 05, 2021
Prizes: $9,450 in prizes!
.png)

Hi,
I recently needed to setup an SSL/TLS configuration in IRIS that supported mutual authentication (where the server IRIS is establish a connection to is verified, and, where IRIS is in turn verified by the remote host). After a bit of research and getting it done, I thought it worthwhile to just go over the process I went through in order to potential help others, and save you some time .
I had in hand, Certificate and Private key for my IRIS instance, that was initiating the connection, and needed to ensure that this was setup correctly.
Hi Developers!
Here're the technology bonuses for the Security Contest 2021 that will give you extra points in the voting:
See the details below.

Hi Community,
We are pleased to invite all the developers to the upcoming InterSystems Security Contest Kick-off Webinar! The topic of this webinar is dedicated to the Security contest.
We’ll discuss the aspects of Security Model implementation in InterSystems IRIS, the requirements, and what do we expect from participants of the Security contest. Also, we’ll answer all the questions related to the contest!
Date & Time: Monday, November 15 — 12:00 AM EDT
Speakers:
🗣 @Andreas Dieckow, Principal Product Manager at InterSystems Corporation
🗣 @Evgeny Shvarov, InterSystems Developer Ecosystem Manager
Good morning -
As we're starting to create more custom message classes to represent out JSON-based integrations, I was pondering how to implicitly grant SELECT privileges to a specific Security Role so they can utilize Message Viewer to search through the message history.
So if all of our custom JSON message classes are under OurParentPkg.Messages.REST.* (e.g., OurParentPkg.Messages.REST.AddPatientRequest and OurParentPkg.Messages.REST.AddPatientResponse), is there a method to ensure that our analysts can be granted the SELECT permission to anything created under OurParentPkg.Messages.
Does Intersystems specifically Ensemble support a Single Sign On architecture? Currently we are using Delegated sign on using LDAP and TLS, however our CIO would like us to move toward a single sign on, so when you sign into your PC it would automatically pass the credentials to Ensemble.
Thanks
Scott
Over the past year or so, my team (Application Services at InterSystems - tasked with building and maintaining many of our internal applications, and providing tools and best practices for other departmental applications) has embarked on a journey toward building Angular/REST-based user interfaces to existing applications originally built using CSP and/or Zen. This has presented an interesting challenge that may be familiar to many of you - building out new REST APIs to existing data models and business logic.
How do you determine what namespace to use for your custom SAML attributes? We want to receive patient context (first name, last name, dob, gender, etc.)
OASIS has resource-id but none of the other attributes. urn:oasis:names:tc:xacml:1.0:resource:resource-id
Does Caché or IRIS have Data Masking capability natively to Test/Dev/Report environment, like other databases?
Hi Community,
Did you know about OWASP and Top Ten Web Application security risks to your Web API or Web Apps?
OWASP is a community foundation created to help us to improve the security of web apps/web APIs. OWASP do the web apps more secure through its community-led open source software projects, hundreds of chapters worldwide, tens of thousands of members, and by hosting local and global conferences.
To summarize the top procedures to do your web app/web api more secure OWASP published the "Top 10 Web Application Security Risks" recomendations, see (source: https://owasp.
When a publish my API, only HTTP is available. How do I publish my REST API using HTTPS?
Hi Team,
I have a requirement to disable the Production Start/Stop buttons for specific support users. But they should be able to stat/stop Ensemble Hosts.
For that new Role, As per documentation along with other Ens resources, I have added %Ens_ConfigItemRun with RWU access and didnt add %Ens_ProductionRun resource.
This makes the Start/Stop buttons disappear from Production Configuration page ( meeting my requirement). But those users are Unable Start/Stop/Restart Ensemble Business Hosts.
There are many options to do a full security scan in your docker images, the most popular option is Anchore community edition.
Anchore will use the main public vulnerabilities databases available, including CVE.
To install Anchore is very ease (source: https://engine.anchore.io/docs/quickstart/), follow the steps:
curl -O https://engine.anchore.io/docs/quickstart/docker-compose.I am getting the following error when trying to fect data from DeepSee:
"Error":"ERROR #5002: Cache error: <PROTECT>%Construct+3^%DeepSee.ResultSet.1 ^DeepSee.Cache.LocalResults(\"session\"),e:\\hs-db\\tfoms\\"
However, I cannot find the place this error points me to.
Specifically, it says 'Label %Construct + 3 lines, in the %DeepSee.ResultSet.1', but there does not seem to be such a place. I could only find the %DeepSee.ResultSet class and it does not have a lable named %Construct.
Hi folks!
Here is how I grant SQL access of user to a particular class/table:
GRANT SELECT, UPDATE ON Packacge_X.Table_Y TO UserZHow can I grant SQL access of a certain user to a whole schema?
When using Studio, ODBC or a terminal connection to Caché or Ensemble, you may have wondered how to secure the connection. One option is to add TLS (aka SSL) to your connection. The Caché client applications - TELNET, ODBC and Studio - all understand how to add TLS to the connection. They just need to be configured to do it.
Configuring these clients is easier in 2015.1 and later. I'm going to be discussing this new method. If you're already using the old, legacy method, it will continue to work, but I would recommend you consider switching to the new one.
In this 3-part series of articles, is shown how you can use IAM to simply add security, according to OAuth 2.0 standards, to a previously unauthenticated service deployed in IRIS.
In the first part, was provided some OAuth 2.0 background together with some IRIS and IAM initial definitions and configurations in order to facilitate the understanding of the whole process of securing your services.
Hello,
fine tuning access permissions is a difficult issue in Caché, at least for me as it seems. More generally, I would be interested in how to find out which permission a user is missing when a permission violation is logged. In this specific case a user, created in (from my point of view) an identical way as on other instances, is not allowed to execute an operation within a CSP service on the messagebank (which however works on the other machines). Unfortunately, the message in the errorlog does not tell where exactly the access violation occurs, or what permission is missing.
During some consulting activity, I found at the client's site CACHEAUDIT database of more than 100 GB size. The reason was simple: several processes produced a great amount of %System/%System/OSCommand audit records due to frequent external calls ($zf(-100,.)). As it is well-known, those events can be easily disabled systemwide, while this can be hardly considered secure enough. Reducing the number of days before audit cleanup from default 62 to some reasonable figure (e.g.
Can a license be reserved for a specific user or group of users? So if I have 20 available licenses, only allow other users to use 19 of them while keeping one open for this specific user?
Hello community,
I would like to report about a security issue, that engages us for some time meanwhile.
We configured a restricted user to read data from a csp page to feed our nagios server with information about configuration items we would like to have an eye upon. The configuration of this user is the same in our production and in our development environment. The called method mainly reads data from lookup tables by sql queries and writes data to a temporary table, which is deleted in the begining.
Hi everybody,
Is there any functionality I could use that triggers real time user-defined code on certain audit events? Right now I am interested in triggering such code on a routine modification event, like the one below. I do know how to access this record programmatically, via %SYS.Audit.
.png)
Thanks in advance,
Anna
Hey Folks,
I am creating my first record map to import a .txt file and eventually create a message outbound. When I try to pull in the sample file I get:
ERROR #5005:
|
|
Any ideas as to why? I have the sample .txt file saved as shown in the available directory. From what I have seen the #5005 error means the file is not available?
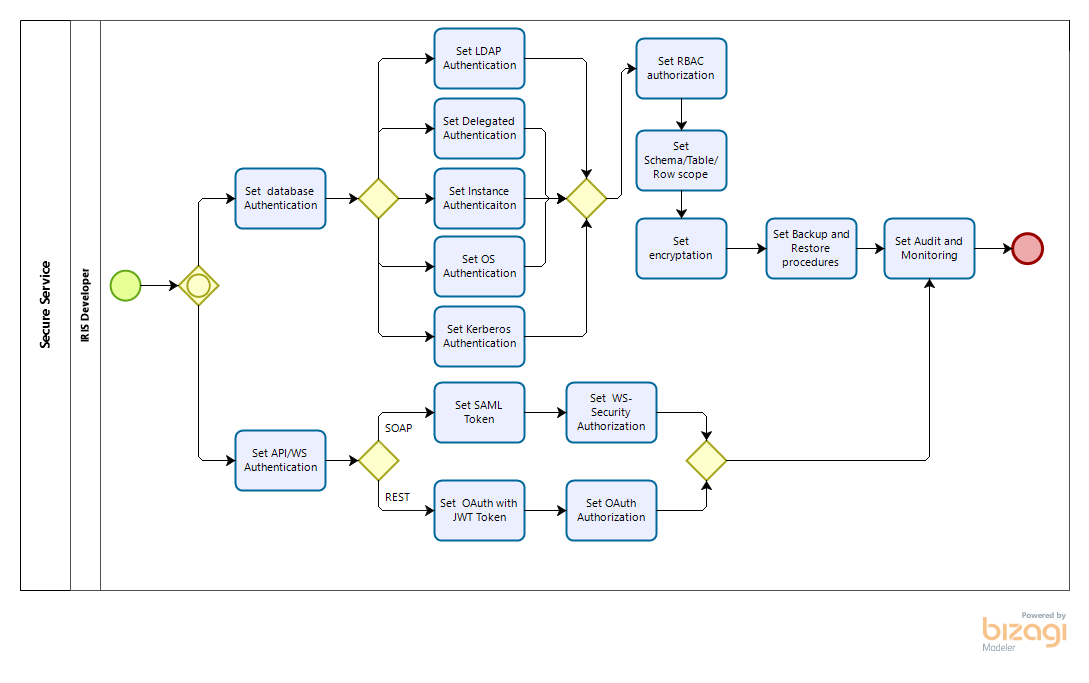
The InterSystems IRIS has two major paths to a digital service: API/Web Service into Interoperability module and multimodel Database/Analytics. Each of them has your security configuration.
To do API security you apply an OAuth or JWT plug-in to the API endpoint. So in the Admin Portal, API producer and consumers get the keys to authenticate the API and consume it. The Admin Portal allows you configure RBAC policies too.
To do WS security the best strategy is to use SAML. In the inbound/outbound SOAP message, include X.
In InterSystems IRIS, the default form of access to the management portal is HTTP, which means that if the client is in the office and the server is in the cloud, many clients probably desire to encrypt their traffic in some way.
Thus, we would like to show you some ways to encrypt your traffic to and from the IRIS management portal (or various REST services) running on AWS.
This article uses the IRIS built-in apache server for access. It should not be used for benchmarking purposes or as a method of access from production environments applications.
Hello, I have an SSL / TLS configuration that used TLSv1.0 encryption.
However, I need to update to the TLS 1.2 version of encryption, and apparently Caché 2012.1 does not support it according to this link: https://community.intersystems.com/post/tls-v12-support-cach%C3%A9
Can I add a library to the Cache, enable TLSv1.2 in some way, or just a version update?
.png)
Hello,
In Caché Management Portal yo can see the SQL privileges per table.
For example : http://localhost:57772/csp/sys/sec/%25CSP.UI.Portal.User.zen?PID=P#3 (Page "SQL Tables").
Is it possible to get them by objectscript or SQL ?
Regards.
Hi Developers!
Want to raise security discussion today!
Let's discuss how InterSystems security for applications works. In general, the concept is clear: we have Resources (what to protect), Roles which combine a set of privileges and accesses to Resources and Users which can have this or that Role.
But there is also a concept of Application which also could have a Role.
So you either provide a Role for a User or for an Application.
What do you use in production? What is your strategy and why? Pros, cons?

“A Dry Martini”, he said. “One. In a deep champagne goblet.”
“Oui, monsieur.”
“Just a moment. Three measures of Gordons, one of vodka, half a measure of Kina Lillet. Shake it very well until it’s ice-cold, then add a large thin slice of lemon peel. Got it?”
"Certainly, monsieur." The barman seemed pleased with the idea.
Casino Royale, Ian Fleming, 1953
OAuth helps to separate services with user credentials from “working” databases, both physically and geographically. It thereby strengthens the protection of identification data and, if necessary, helps you comply with the requirements of countries' data protection laws.
With OAuth, you can provide the user with the ability to work safely from multiple devices at once, while "exposing" personal data to various services and applications as little as possible. You can also avoid taking on "excess" data about users of your services (i.e. you can process data in a depersonalized form).
By default InterSystems IRIS expose your endpoints using http, but can be necessary run https from your dev env and/or get public internet access to your app. You can buy or get a certificate and config a gateway, spending many hours or use a great public service called ngrok. Follow the steps:
1 - Run your app, I will use FHIR template as sample, see:
1.1 download the app: git clone https://github.com/intersystems-community/iris-fhir-template.git
1.2 go to the app dir: cd iris-fhir-template
1.3 run the app: docker-compose up -d
1.