Hi everyone,
I'm trying to figure out how to automatically resend a message using a business operation.
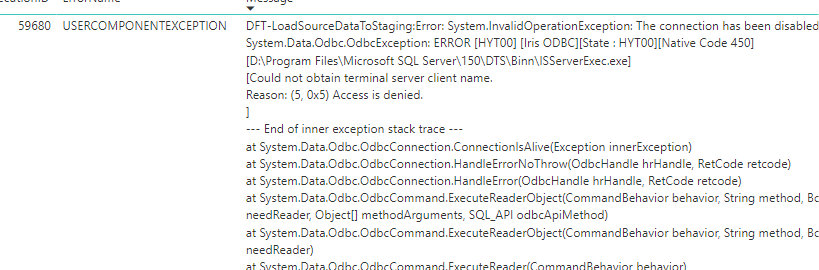
I'm working on a production where HTTP messages are sent from a Business Component to the URL of a Postman Mock Service and I'd like to understand what I can do when the server doesn't respond within a certain timeout. To test this situation, I created a Business Operation component called "Sender", with an "EnsLib.HTTP.OutboundAdapter", which is sending an HTTP message via a POST request to the Mock Server. To create the message, I defined a %Net.