Hey Developers,
Watch this video to learn about the analytics approach to InterSystems IRIS encryption and how it interacts with in-storage data compression and deduplication compared to storage-level encryption:
In cryptography, encryption is the process of encoding a message or information in such a way that only authorized parties can access it and those who are not authorized cannot.
Hey Developers,
Watch this video to learn about the analytics approach to InterSystems IRIS encryption and how it interacts with in-storage data compression and deduplication compared to storage-level encryption:
Hi Community,
Enjoy the new video on InterSystems Developers YouTube:
⏯ Ahead of the Threats - The Future of Secure Systems @ Ready 2025
IRIS can use a KMS (Key Managment Service) as of release 2023.3. Intersystems documentation is a good resource on KMS implementation but does not go into details of the KMS set up on the system, nor provide an easily followable example of how one might set this up for basic testing.
The purpose of this article is to supplement the docs with a brief explanation of KMS, an example of its use in IRIS, and notes for setup of a testing system on AWS EC2 RedHat Linux system using the AWS KMS. It is assumed in this document that the reader/implementor already has access/knowledge to set up an AWS EC2 Linux system running IRIS (2023.3 or later), and that they have proper authority to access the AWS KMS and AWS IAM (for creating roles and polices), or that they will be able to get this access either on their own or via their organizations Security contact in charge of their AWS access.
What is JWT?
JWT (JSON Web Token) is an open standard (RFC 7519) that offers a lightweight, compact, and self-contained method for securely transmitting information between two parties. It is commonly used in web applications for authentication, authorization, and information exchange.
A JWT is typically composed of three parts:
1. JOSE (JSON Object Signing and Encryption) Header
2. Payload
3. Signature
These parts are encoded in Base64Url format and concatenated with dots (.) separating them.
Hello,
I am currently facing the task of retrieving or sending HL7 messages from a web API. Since we only send HL7 messages via internal sockets, web APIs are relatively new to me.
The following is my plan for the new interface:
I have created a new custom business service that periodically sends requests to a business process. In this business process, the HTTP request (HTTP.GenericMessage) is then created from scratch. The special feature is the "Authorisation" header field, where a signature is inserted, which consists of a base64-encoded hash value.
TLS, the successor to SSL, stands for Transport Layer Security and provides security (i.e. encryption and authentication) over a TCP/IP connection. If you have ever noticed the "s" on "https" URLs, you have recognized an HTTP connection "secured" by SSL/TLS. In the past, only login/authorization pages on the web would use TLS, but in today's hostile internet environment, best practice indicates that we should secure all connections with TLS.
So, why would you implement TLS for HL7 connections?
.png)
I am giving this distraction the code name "Compliment Sandwich" for a reason yet to be realized, but I'd rather the community go right for the jugular shooting holes in a solution that implements wireguard based connectivity for our workloads in general, as I would like to refine it as a fall project leading up to KubeCon in Atlanta and if I miss the mark, Ill get it done before Amsterdam.
I have an application that is requires an Encoded HL7 message sent over SOAP over HTTPS using SSL/TLS... the Response that is return is also encoded, which I know how to Decode but not sure when I Decode the response how to Extract the HL7 message to send back to the router.
How do I capture the Routing Source System and parse the encoded message back into an HL7 format that would show on the trace viewer?
Below is an example...where I get the response and want to send it back to FeederScottRouting as an HL7 message that can be tied to the Parent ID of the sending request message?
.png)
For my hundredth article on the Developer Community, I wanted to present something practical, so here's a comprehensive implementation of the GPG Interoperability Adapter for InterSystems IRIS.
Every so often, I would encounter a request for some GPG support, so I had several code samples written for a while, and I thought to combine all of them and add missing GPG functionality for a fairly complete coverage. That said, this Business Operation primarily covers data actions, skipping management actions such as key generation, export, and retrieval as they are usually one-off and performed manually anyways. However, this implementation does support key imports for obvious reasons. Well, let's get into it.
Dear Community,
I am trying to convert a base64 encoded string to a pdf. I have tried a lot of possible ways, but never succeeded. I am able to decode the base64 using $System.Encryption.Base64Decode but I am not able to convert it and store this in a path.
Can anybody help me out here?
Thanks.
Working on a project where I'm needing to make FHIR calls from my HealthConnect Interop production to Epic.
My issue is I'm not able to construct a valid JWT for the OAuth token retrieval that Epic will accept. I have the below code where I'm able to create a valid header and payload that I'm base64URL encoding and then trying to sign with my .pem private key file. However, Epic is not liking the signature portion of my JWT.
As such, I wanted to present my code to see if I'm performing the signature steps correctly? I've seen some posts where the %Net.
I need to create a JWT to connect to EPIC FHIRserver sandbox.
https://fhir.epic.com/Documentation?docId=oauth2§ion=BackendOAuth2G…
You will generate a one-time use JSON Web Token (JWT) to authenticate your app to the authorization server and obtain an access token that can be used to authenticate your app's web service calls. There are several libraries for creating JWTs. See jwt.io for some examples.
The header and payload are then base64 URL encoded, combined with a period separating them, and cryptographically signed using the private key to generate a signature.
Hey Developers,
Watch this video to discover an analytical approach to InterSystems IRIS encryption and how it interacts with storage compression and deduplication compared with storage-level encryption:
⏯ Encryption Landscape for Data at Rest @ Global Summit 2023
I want to generater a license for my code,but i don`t how to get CpuID and diskid in iris,someone know?
Hi guys,
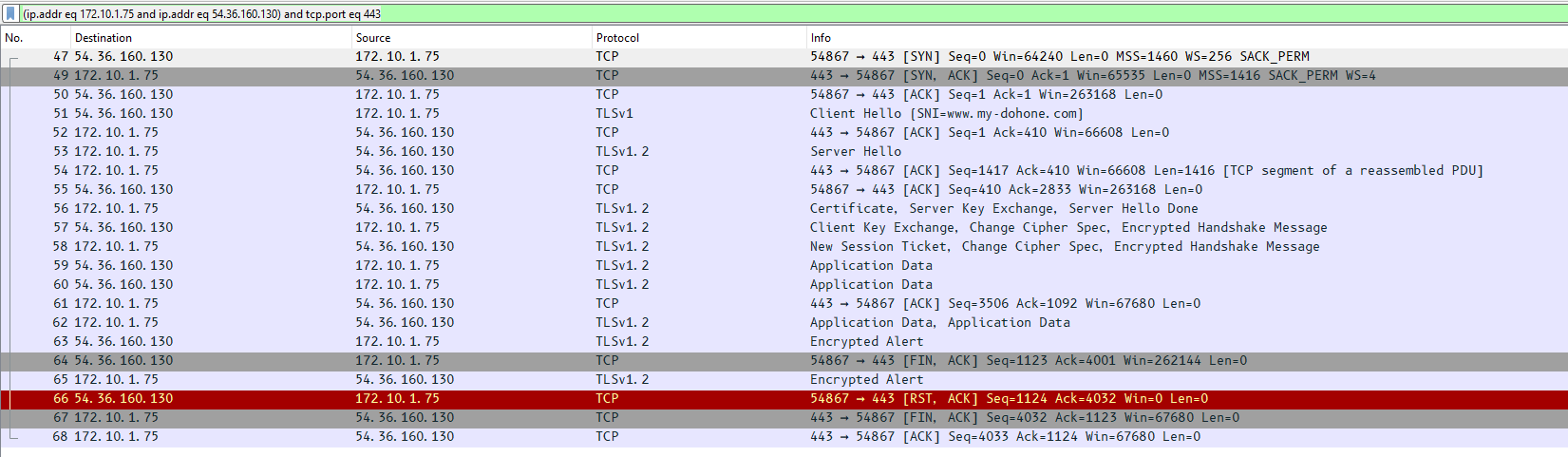
I need to check my HTTPS POST REQUEST, in order to do this I try to catch it by using wireshark.
I can't see anything because of the encryption.
I try unsuccefully to use the SSLKEYLOGFILE key (windows 11), but the generated file did not increase when I trigger my code OR postman, it grows only by the action of the web browser.
My question is so simple :
1°) How have a clear view of the HTTPS request from IRIS code in wireshark
2°) Why the keylog file did not increase when trigger the code from IRIS ?
Hi guys,
I try to make a test of encryption, decryption of a simple text.
I can crypt my text, but I can't decrypt it, do you see somewhere a dummy error of my part ?
Thanks for help
ClassMethod UnitTest()
{
set inputPlainText = "David"
// get private key
set privKeyFileName = "C:\temp\toto.pem"
set privobjCharFile = ##class(%Stream.FileCharacter).%New()
set privobjCharFile.Filename = privKeyFileName
set privKey = privobjCharFile.Read()
set Inputbase64 = $SYSTEM.Encryption.Base64Encode(inputPlainText)
// encrypte text using RSA
set encryptText = $System.Encryption.
I want to use AESEncode encryption, but it prompts a MAXSTRING error. How to solve it?
Hello all,
we have an encryption problem.
Out partner decode url with AES CBC 256 using crypto-js
https://community.dynatrace.com/t5/Troubleshooting/AES-Encryption-and-D…
with this params value:
var iv = CryptoJS.enc.Hex.parse("0000000000000000");
var stringyouWantToEncrypt = "HelloWorld";
var base64Key = "RXJjb2xpbm9zZW1wcmVpbnBpZWRp";
var encrypted = CryptoJS.AES.encrypt(
stringyouWantToEncrypt,
CryptoJS.enc.Base64.parse(base64Key),
{
iv: iv,
}
);
console.log("Key " + CryptoJS.enc.Base64.parse(base64Key));
console.log("Result!
Hi Community,
Can I please check what the size limit for the parameter in $SYSTEM.Encryption.Base64Decode() method ?
I have a 12 page base64 encoded PDF document, which is failing when decoded. I am getting the error below:
ERROR <Ens>ErrException: <ILLEGAL VALUE>zXSDToLogical+1^%Library.Binary.1 -- logged as '-' number - @''
OBX:5 size=4233781
I tried the below from terminal, but it is not able copy the whole string for the parameter so couldn't execute it.
Set text=$SYSTEM.Encryption.Base64Decode("JVB<<TRUNCATED>>)
I am able decode the same string using notepad++ and save it as PDF.
We've implemented SAML authentication for our application where we are the service provider and various other entities are the identity providers. We've done successful connections with several identity providers including Okta, Duo Mobile, Ping Identity, and Azure. Validating the SAML response with signed assertions has been working great. Now, I am trying implement support for the SAML assertions in the response being encrypted for a new identity provider and struggling to understand procedurally how to go about this.
Several steps should be done in order to secure the connection through xDBC clients to an IRIS Server instance using TLS. Most of the information can be obtained from the documentation about TLS on IRIS here, about configuring the security layer for encrypted connections. In the next paragraphs we will cover an step-by-step guide on how to configure and test the connection using SQL Clients apps using ODBC and JDBC.
In this article, we will establish an encrypted JDBC connection between Tableau Desktop and InterSystems IRIS database using a JDBC driver. While documentation on configuring TLS with Java clients covers all possible topics on establishing an encrypted JDBC connection, configuring it with Tableau might be a little bit tricky, so I decided to write it down.
Before we start with client connections, you need to configure SuperServer, which by default runs on port 1972 and is responsible for xDBC traffic to accept encrypted connections.
I have a compactJWE that I want to decrypt using a key. I read the key from a .pem file and create a JWK with "RSA-OAEP" algorithm. I have the code below in a routine (.mac) file.
decryptJWE
#include %msqlsWhen I run it in the terminal, the previous status checks return "1" and I can also see the Objects, until the jwe.Decrypt part (jweDecryptStatus), where it returns "0" with the error message "ERROR #9723: Unsupported JOSE algorithm: A256GCM". The encrypted JWT comes from the other source, and I have no choice but to use the A256GCM algorithm.
So I have a base string that I want to sign using RSA-SHA256. I have a .p12 file and passphrase to get the RSA Private key using NodeJS (pem.readPkcs12 library), which I don't know how to do that in intersystems as well. (would appreciate if you can include a solution for that too)
The main problem here is I am trying to sign a string and print the result to terminal, using the code below in a routine (.mac file).
Hi All,
Hopefully someone can help me with this case. I need to encrypt a text(querystring) with an AES265 encryption. An other vendor is decrypting this information. I have a working class in C#. I've tried to build the same in Objectscript for the encrypt part but there's a missing link somewhere. What's the difference between the C# and Objectscript implementation?
Objectscript code (until now):
Class// Symmetric Keys sample to encryptClassMethodThis give this as example output:
.png)
Hi,
We wanted to use the MD5Hash function,
And had trouble understanding it's return value , as documented:
"Return value: 16-byte MD5 hash."
The value we wanted should have been a simple string, and we did not know how to convert the output to string.
Searching for a solution we found this article:
https://groups.google.com/forum/#!msg/intersystems-public-cache/FdkHIgS9PkQ/P7s-92kN70UJ
That had this solution that works:
"If you know what this gibberish stuff is about, it can be very simple ;)
USER> s h = ##class(%SYSTEM.Encryption).
Credentials for a Productions are stored as plain text in ^Ens.SecondaryData.Password and exposed as plain text via SQL table Ens_Config.Credentials which is not ideal as only admins should know the credentials.
I can create my own adapter etc... to store and use encrypted passwords but does anyone know if there is a standard way to do this in a Production?
Alternatively, am I missing how to secure this so the production can run and someone can monitor and operate a production without access to the SQL table or global?
Hi! I'm banging my head to the wall with HMAC authentication. I have tried to implement this various ways but nothing seems to work.
If someone could help on this it would be great!
Here is a code that I have tried and working Javascript example, tested on Postman.
Set requestTimeStamp = $ZDATETIME($HOROLOG,-2)
Set nonce = ..getRandomString()
Set signatureRawdata = Appid_requestTimeStamp_nonce
Set keyUTF8 = $zconvert(Appkey,"O","UTF8")
Set signatureRawdataUTF8 = $zconvert(signatureRawdata,"O","UTF8")
Set tSigningKey = $SYSTEM.
Currently running Ensemble on Red Hat Enterprise Linux Server release 7.7
One of our clients is requesting files sent to their SFTP site be encrypted with their PGP public key and digitally signed with our PGP private key
We have created a custom class that includes the following command to encrypt the files
if (pAction = "Encrypt") {
// Find the Key ID from the Keyname
set tKeyId = ..GPGKeyLookup(pKeyName, ..#PUBLICKEYLUT)
set tCmdLine = "gpg --homedir "_pGPGhomedir_" --always-trust -r """_tKeyId_""" -o "_pOutFileName_" -e "_pInFileName
}
// Execute the command to generate the output file
I need to store an equivalent of the SNN (Social Security number). I need it to be encrypted and I'll have to be able to search for it once stored.
For what I've seen my options are:
- SHAHash from the %system.encryption library. Simple and easy to implement. My question is, might collisions be a problem? We are talking about a 10 millions entry.
- AES encryption. In this case I'd like to know if there is a standard way for key management in the InterSystems environment.
I can eventually get a certificate for this project to use other encryption function as well.
Open to suggestions.