Background
For a variety of reasons, users may wish to mount a persistent volume on two or more pods spanning multiple availability zones. One such use case is to make data stored outside of IRIS available to both mirror members in case of failover.
Kubernetes (commonly stylized as k8s) is an open-source container-orchestration system for automating application deployment, scaling, and management. It aims to provide a platform for automating deployment, scaling, and operations of application containers across clusters of hosts. It works with a range of container tools, including Docker.
For a variety of reasons, users may wish to mount a persistent volume on two or more pods spanning multiple availability zones. One such use case is to make data stored outside of IRIS available to both mirror members in case of failover.
For a variety of reasons, users may wish to mount a persistent volume on two or more pods spanning multiple availability zones. One such use case is to make data stored outside of IRIS available to both mirror members in case of failover.
Hi!
We are working on containerizing our IRIS product. We want to extract the message log that is shown in the terminal, but if possible, we want to format the output as JSON and include some extra fields from the instance to enhance our monitoring. Is this possible?
Any guide or example about it?
Thanks!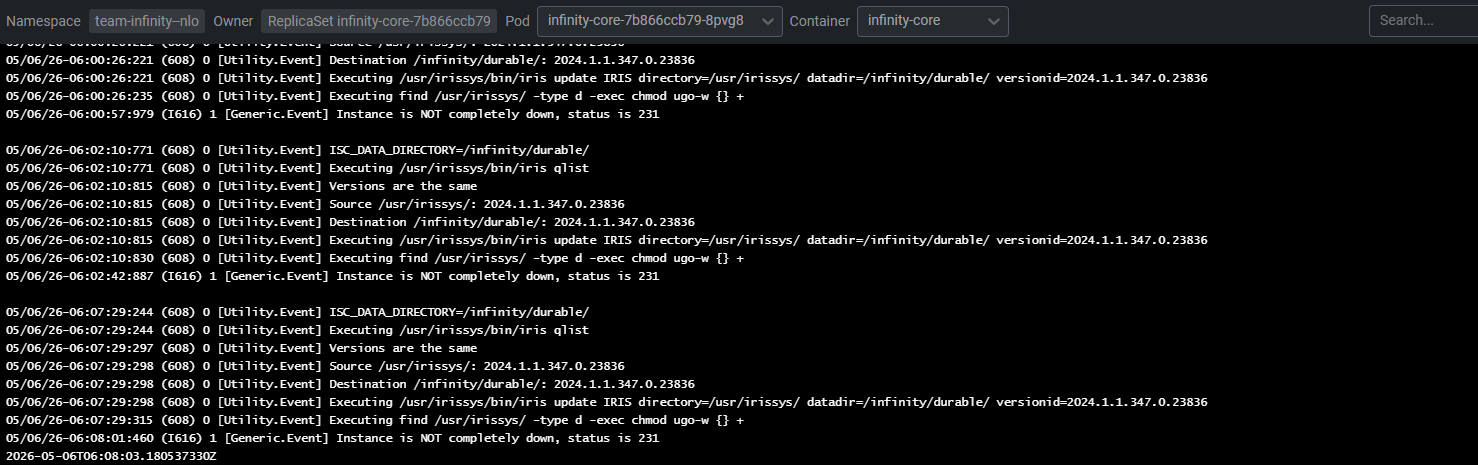
Hi!
We are deploying the iris image in a Kubernetes environment and the cluster state is "Hung" , looking the alerts endpoint we get 2 alerts:
[
{
"time":"2026-03-24T13:45:44.548Z",
"severity":"2",
"message":"System appears to have failed over from node a69a9f137593"
},
{
"time":"2026-03-24T13:46:30.274Z",
"severity":"2",
"message":"Error: <PROTECT>KillAlive+1^%SYS.CDIRECT in SERVERS"
}
]
Any idea / help where those are comming from and how to address them?
We are trying to run the HS solution inside of a container, but we are getting the following errors un start up
03/17/26-10:19:05:108 (1386) 1 [Generic.Event] Cannot lock /usr/irissys/mgr/hslib/ err(13): will try accessing readonly
03/17/26-10:19:08:174 (1386) 1 [Generic.Event] Cannot lock /usr/irissys/mgr/enslib/ err(13): will try accessing readonly
I understand that those databases should be mounted as read only don't needing the lock, any idea how to fix it? or where should I look to configure it correctly?
Thanks!
.png)
For those of us building InterSystems workloads on Kubernetes, we are definitely spoiled with the InterSystems Kubernetes Operator (IKO) doing the heavy lifting and mirroring on day one. Where us spoiled brats jump up and down is when we try to add additional databases/namespaces when we provision from HealthConnect containers on day two, while others get to utilize HealthShare Mirroring for this task, the prerequisite of mirroring HSSYS out of the gate has been somewhat elusive. Here is example on how you can this powerful feature up and running with the employment of IKO and IrisClusters.
.png)
A few days before Kubecon, the external-secrets-operator went GA with 1.0.0 and is set to ride shotgun for Kubernetes Secrets Management and put Vault in the backseat. You can glance at the "Providers" list for the solution and immediatley understand that you can leave the "which Secrets Manager" conversation to others while you do your job utilizing external secrets on your IrisCluster workloads, which by my count with the operator and a single IrisCluster is more than a fistful of secrets of different types, even under a single tenant. So let them sprawl, the secrets managers that is, not the secrets.
.png)
If you're running IRIS in a mirrored IrisCluster for HA in Kubernetes, the question of providing a Mirror VIP (Virtual IP) becomes relevant. Virtual IP offers a way for downstream systems to interact with IRIS using one IP address. Even when a failover happens, downstream systems can reconnect to the same IP address and continue working.
The lead in above was stolen (gaffled, jacked, pilfered) from techniques shared to the community for vips across public clouds with IRIS by @Eduard Lebedyuk ...
Articles: ☁ vip-aws | vip-gcp | vip-azure
This version strives to solve the same challenges for IRIS on Kubernetes when being deployed via MAAS, on prem, and possibly yet to be realized using cloud mechanics with Manged Kubernetes Services.
.png)
Hello cpf fans! This distraction I used the "seed" capability in IRIS to provision an entire IrisCluster mirror, 4 maps wide with compute starting from an IRIS.DAT in a galaxy far far away. This is pretty powerful if you have had a great deal of success with a solution running on a monolithic implementation and want it to scale to the outer rim with Kubernetes and the InterSystems Kubernetes Operator. Even though my midichlorian count is admittely low, I have seen some hardcore CACHE hackers shovel around DATS, compact and shrink and update their ZROUTINES, so this same approach could also be helpful shrinking and securing your containerized workload too. If you squint and feel all living things around you, you can see a glimpse of in place (logical) mirroring in the future as a function of the operator and a migration path to a fully operational mirrored Death Star as the workload matures.
.png)
Here is an option for your headspace if you are designing an multi-cluster architecture and the Operator is an FTE to the design. You can run the Operator from a central Kubernetes cluster (A), and point it to another Kubernetes cluster (B), so that when the apply an IrisCluster to B the Operator works remotely on A and plans the cluster accordingly on B. This design keeps some resource heat off the actual workload cluster, spares us some serviceaccounts/rbac and gives us only one operator deployment to worry about so we can concentrate on the IRIS workloads.
.png)
If you are in the business of building a robust High Availability, Disaster Recovery or Stamping multiple environments rapidly and in a consistent manner Karmada may just be the engine powering your Cloning Facility.
.png)
Rancher Government Hauler streamlines deploying and maintaining InterSystems container workloads in air-gapped environments by simplifying how you package and move required assets. It treats container images, Helm charts, and other files as content and collections, letting you fetch, store, and distribute them declaratively or via CLI — without changing your existing workflows. Meaning your charts and what have yous, can have conditionals on your pull locations in Helm values, etc.
If you have been tracking how HealthShare is being deployed via IPM Packages, you can certainly appreciate the adoption of OCI compliance storage for the packages themselves using ORAS... which is core to the Hauler solution.
.png)
KWOK, Kubernetes WithOut Kubelet, is a lightweight tool that simulates nodes and pods—without running real workloads—so you can quickly test and scale IrisCluster behavior, scheduling, and zone assignment. For those of you wondering what value is in this without the IRIS workload, you will quickly realize it when you play with your Desk Toys awaiting nodes and pods to come up or get the bill for provisioning expensive disk behind the pvc's for no other reason than just to validate your topology.
Here we will use it to simulate an IrisCluster and target a topology across 4 zones, implementing high availability mirroring across zones, disaster recovery to an alternate zone, and horizontal ephemeral compute (ecp) to a zone of its own. All of this done locally, suitable for repeatable testing, and a valuable validation check mark on the road to production.
For a variety of reasons, users may wish to mount a persistent volume on two or more pods spanning multiple availability zones. One such use case is to make data stored outside of IRIS available to both mirror members in case of failover.
.png)
I am giving this distraction the code name "Compliment Sandwich" for a reason yet to be realized, but I'd rather the community go right for the jugular shooting holes in a solution that implements wireguard based connectivity for our workloads in general, as I would like to refine it as a fall project leading up to KubeCon in Atlanta and if I miss the mark, Ill get it done before Amsterdam.
.png)
Though trivial, Id like to go multi-cloud with the stretched IrisCluster for a couple of reasons to socialize the power of Wireguard when it supplies the network for a properly zoned IrisCluster by adding another mirror role to Amazon Web Services in the Western United States based datacenter in Oregon.
#InterSystems Demo Games entry
Kubernetes horizontal pod auto-scaling (HPA) is the key to handle the unpredictable compute workload in healthcare systems. IKO helps orchestrating the IRIS container deployment in Kubernetes including the capability to configure HPA. This demo uses XSLT processing as an example to showcase this type of elasticity.
🗣 Presenter: @Simon Sha, Sales Architect, InterSystems
InterSystems Kubernetes Operator (IKO) 3.8 is now Generally Available. IKO 3.8 adds new functionality along with numerous bug fixes and security updates. Highlights include:
Follow the Installation Guide for guidance on how to download, install, and get started with IKO. The complete IKO 3.8 documentation

Just like a knockout punch, without giving the opponent a chance, Kubernetes, as an open source platform, has a universe of opportunities due to its availability (i.e., the ease of finding support, services and tools). It is a platform that can manage jobs and services in containers, which greatly simplifies the configuration and automation of these processes.
But let's justify the title image and give the tool in question the “correct” name: InterSystems Kubernetes Operator.