How to execute terminal commands from a webpage
Now, let’s say you can’t access the terminal or simply you just rather execute it from a web interface. In this article, I will show you how to execute terminal commands from a simple web page.
For example, in the image below you see how we execute $zv on a webpage:
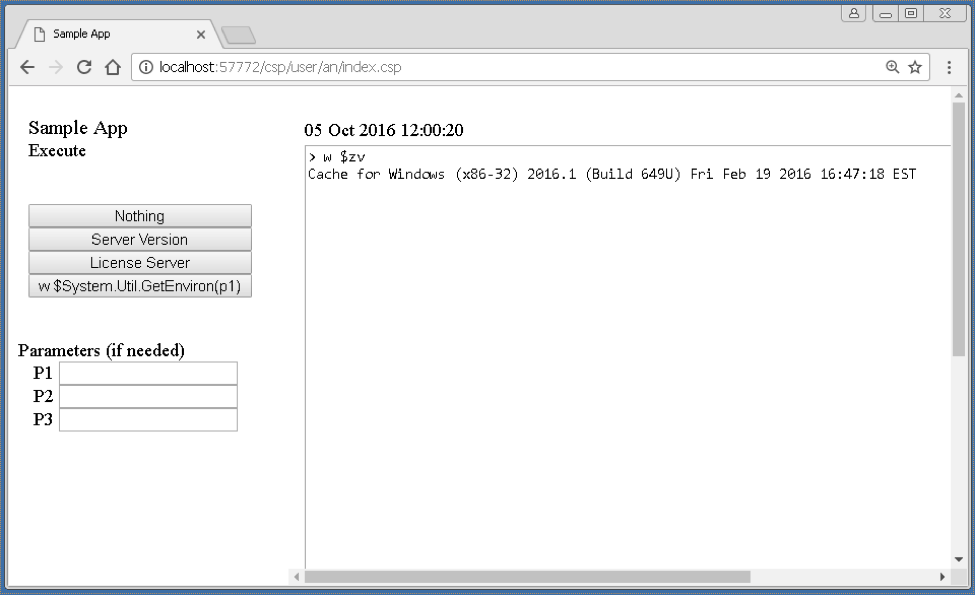
This is mostly possible due to the XECUTE command in Caché ObjectSCript. This command takes a string as a parameter and tries to execute it. This is the command used from the webpage, to execute what is being passed from the left navigation menu.
This article contains three snippets of code. Each of which corresponds with a separate file. In total, there are three files:
1. Index.csp (A sample page with two frames):
<HEAD><TITLE> Sample App </TITLE></HEAD>
<FRAME name=Navigation src="leftMenu.csp" noResize>
<FRAME name=mainFrame src="execute.csp">
</FRAMESET>
2. leftMenu.csp (self-explanatory):
<HEAD><TITLE>Left Menu </TITLE><LINK REL="stylesheet" TYPE="text/css" HREF="" TITLE="Standard Style" ></HEAD>
<BR> <FONT SIZE=+1>Sample App</FONT><BR> Execute <BR><BR><BR>
<FORM ACTION="execute.csp" TARGET="mainFrame" METHOD="GET">
<INPUT TYPE=SUBMIT VALUE="Nothing" STYLE="width:200;" onclick="document.forms[0].command.value = '';" title="()"> <BR>
<INPUT TYPE=SUBMIT VALUE="Server Version" STYLE="width:200;" onclick="document.forms[0].command.value = 'w $zv';"> <BR>
<INPUT TYPE=SUBMIT VALUE="License Server" STYLE="width:200;" onclick="document.forms[0].command.value = 'Do $System.License.ShowServer()';"> <BR>
<INPUT TYPE=SUBMIT VALUE="w $System.Util.GetEnviron(p1)" STYLE="width:200;" onclick="document.forms[0].command.value = 'w $System.Util.GetEnviron';"> <BR>
<BR><BR> Parameters (if needed)<BR>
P1 <INPUT TYPE=TEXT NAME="param1" VALUE=""><BR>
P2 <INPUT TYPE=TEXT NAME="param2" VALUE=""><BR>
P3 <INPUT TYPE=TEXT NAME="param3" VALUE=""><BR>
3. execute.csp (right-hand frame where we execute the code and redirect the output:
<HTML><HEAD><LINK REL="stylesheet" TYPE="text/css" HREF="" TITLE="Standard Style" ><TITLE>Execute </TITLE></HEAD>
<SCRIPT LANGUAGE=CACHE RUNAT=SERVER>set t1 = $piece($h,2)</SCRIPT>
<TR><TD></TD><TD><BR>#($zdt($h,2))#</TD></TR>
<TEXTAREA COLS="110" ROWS="45">
if %request.Get("command") '= "" {
set parens = 0
set cmd = %request.Get("command")
if %request.Get("param1") '= "" set cmd = cmd_"("_%request.Get("param1"), parens=1
if %request.Get("param2") '= "" set cmd = cmd_","_%request.Get("param2")
if %request.Get("param3") '= "" set cmd = cmd_","_%request.Get("param2")
if (parens=1) set cmd = cmd_")"
w "> "_cmd,!
}
if %request.Get("command") '= "" {
xecute cmd
}
</SCRIPT>
</TEXTAREA></TD></TR>
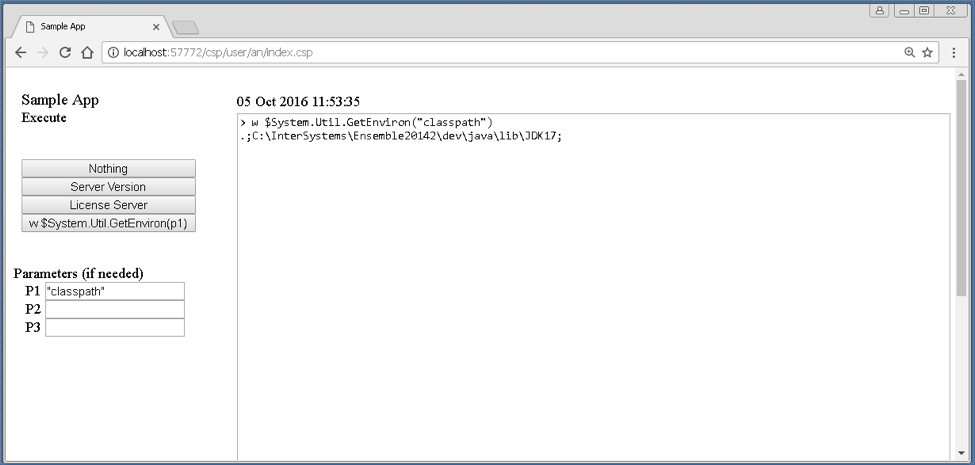
You can also pass parameters if you need to. See example below.
Here is the source code.
Hope you find it useful !
Comments
You could go a further step and run a JavaScript-based terminal console in a browser and hooking it up to Cache via Node.js.
See https://robtweed.wordpress.com/2014/03/03/ewd-js-and-vista-adding-a-jav… for an example implementation
These days, you could use something like Electron to create what appears to be a Windows application, but in fact is a packaged up Chrome & Node.js environment. In fact, IMO, this is how Atelier should have been implemented.
Remember that as soon as you have something such as this running in a browser, security (ie who has / hasn't access to the application running in the browser) becomes a major issue - you're giving command-line access to your Cache database!
I concur the warning about security implications once you've exported terminal access via unauthorized CSP application.
This is very big, and very wide security hole! One could escalate their permissions to localsystem superuser (when you run Windows) and could do pretty much anything with your system, if you didn't properly lock all involved layers.
There is also WebTerminal project.
I guess imitation is the sincerest form of flattery...
Of course, Security has to be taken into account !
BTW, Caché Web Terminal now has intelligent code completion for classes and methods "on the fly" in the latest release, very nice feature.
@Jose Ruperez ! Your article is in top-5 most viewed through the whole history of Developer Community with 29K reads! Thank you very much! And, please, write more! :)