Authentication options for Caché REST Application
Hi, Community!
Suppose If you develop a client js application which works with Caché server via REST API (CSP Gateway).
What are the options for Authentication and working with Caché session then?
Comments
Evgeny, consider using OAuth2 with OpenID Connect as the first choice.
Dan
Hi, Dan!
Sure, it is the option, thank you! And I can mention your series of posts with the step-by-step implementation of it.
Sergey, thank you for the thorough answer!
Then, in your client app settings
Do you mean web-app settings like in the following screenshot?
But why not using basic authentication? Can I consider using it?
Hi!
You can use custom Caché Login Page as the simplest solution.
Suppose, you have React (it doesn't matter anyway) csp-application as a client and you need to authenticate single user at time.
You can create login.csp page somewhere in your project and set it as custom login page. Content could be like this (basic implementation, styles not included):
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="utf-8">
<meta http-equiv="X-UA-Compatible" content="IE=edge">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>Caché Login</title>
</head>
<body>
<div id="login">
<div>
<div>
<form name="Login" method="post">
<div>
<div>
<div>
<input type="text" placeholder="Login" name="CacheUserName">
</div>
</div>
<div>
<div>
<input type="password" placeholder="Password" name="CachePassword">
</div>
</div>
<button type="submit">Log in
</button>
#($select( ($Get(%request.Data("Error:ErrorCode",1))'="")&&($$$GETERRORCODE($Get(%request.Data("Error:ErrorCode",1)))'=$$$ERRORCODE($$$RequireAuthentication)): "<div>The user name or password is incorrect</div>", 1:"") )#
</div>
</form>
</div>
</div>
</div>
</body>
</html>
You can change the content of this page to match your application look and logic. You can include any 3rd-party scripts and styles.
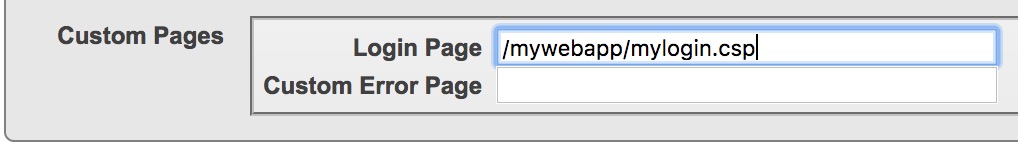
Then, in your client app settings (Management Portal) set recently created login.csp page as custom login page. Also, set Allowed Authentication Methods to "Password" and Session Cookie Path to the same value for both client and rest applications.
After user will be authenticated, browser will use Cookies. You can log out from application just by redirecting user to current URL with ?CacheLogout=1 appended. You can also reload the page each %session.AppTimeout)#' + 15) * 1000 ms to automatically redirect user to login page if session is closed (don't forget to reset this counter after rest requests or/and send some sort of throttled ping after user interactions).
Do you mean web-app settings like in the following screenshot?
Yes.
But why not using basic authentication? Can I consider using it?
It's way better to use CLP because this way Caché tracks authorization and licenses and you don't need to think about it in your app.
Here's some recommendations on securing REST + CSP web apps:
- All brokers effectively have Parameter UseSession = 1;
- REST web application and client web application allow only authenticated (i.e. password) access.
- REST web application and client web application have reasonable Session timeout (i.e. 900, 3600).
- REST web application and client web application have the same GroupById value.
- REST web application and client web application have the same cookie path.
Client web application can have a custom Login Page (or just use default login page, that's okay too).
Thanks, Eduard!
This is very helpful.
May I ask, what are the caveats using basic authentication instead of CLP (Caché Login Page)?
You'll need to:
- write authorization code
- control current authorization state
- check that it all works as expected so you don't consume more that one license per user
There's no reason to do that, as standard Caché tools, such as Login page provide all required capabilities.
Does accessing the login page creates a session and uses a license? Or only after authenticated?
Only after authenticated.